AZ-104 - Topic 03 -Securing Data Access with Microsoft Entra Conditional Access Policies
Scenario
Since I come from the healthcare industry, I’d like to use a healthcare-related example to explain Microsoft Entra Conditional Access.
In healthcare, safeguarding patient data is of utmost importance. Imagine a hospital’s IT team managing remote access for administrators who need to log in securely from various locations. How can they ensure that only authorized personnel access sensitive data while minimizing security risks? This is where Microsoft Entra Conditional Access becomes essential.
Problem Statement
In my previous articles, I used UnityCare Health as an example name, and I will continue to do so. These names are purely illustrative and do not represent any real hospitals or laboratories. The hospital has a team of Global Administrators responsible for managing its cloud infrastructure. These admins often work remotely, accessing Azure AD from various locations.
The IT security team has identified below risk:
- Some administrators connect from untrusted locations, which could be a security threat.
- A compromised admin account could expose patient records and hospital systems.
To mitigate risks, the hospital wants to enforce the following security measures:
- Multi-Factor Authentication (MFA) for all Global Administrators.
- Only allow access from trusted (hospital-owned) Azure AD-joined devices.
- Block or challenge access from untrusted locations.
The IT team first attempted to secure admin accounts by modifying MFA user settings from the Multi-Factor Authentication page in Azure AD. However, this approach failed to meet the security requirements because, It only enforced MFA but did not restrict access based on device compliance or location. And, Administrators could still log in from personal or unauthorized devices.
Secure Access Anywhere: How Microsoft Entra ID Protects Your Data
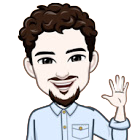
Imagine a hospital where a Global Admin needs to access sensitive medical data. They can use either a hospital laptop (trusted device) or a personal laptop (untrusted device) from different locations.
To ensure security, Microsoft Entra ID (formerly Azure AD) applies Conditional Access Policies,like security guards checking different factors before granting access.
How does it work?
1 - Who is trying to access?
- A Global Admin logs in.
2 - From which device?
- If it’s a Hospital Laptop (Trusted) → ✅ More likely to get access.
- If it’s a Personal Laptop (Untrusted) → 🚫 Extra security checks needed.
3 - From where?
- Trusted Location (e.g., Hospital Network) → ✅ Access more likely.
- Untrusted Location (e.g., Home, Public Wi-Fi) → 🚫 Extra security required.
4 - Security Checks (Conditional Access Policies):
- MFA (Multifactor Authentication) → Enter a code from a phone.
- Device Compliance Check → Ensure security settings are correct.
- Location-based Access → Ensure login is from a safe place.
5 - Final Decision:
- ✅ If all conditions are met → Access Granted
- ❌ If any condition fails → Access Denied
Correct Approach: Implementing a Conditional Access Policy
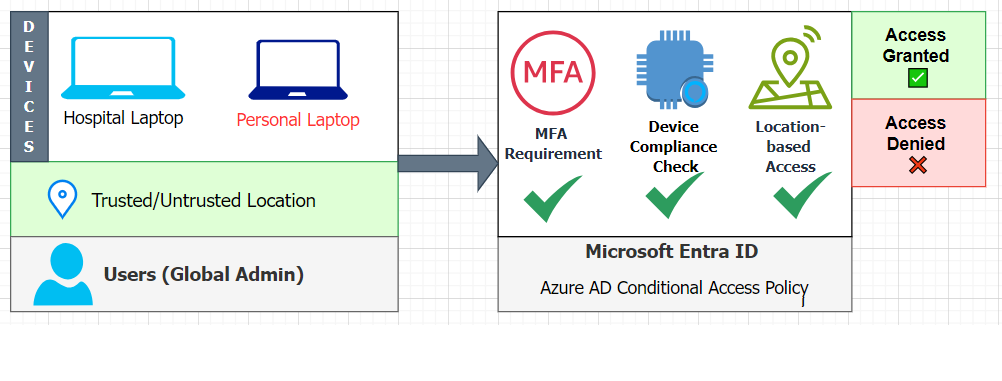
1 - Sign in to Microsoft Entra Admin Center
- Go to Microsoft Entra ID.
- Sign in with Global Administrator credentials.
- Create a New Conditional Access Policy
2 - Navigate to Protection → Conditional Access.
- Click + New policy and provide a descriptive name (e.g., “Global Admins Secure Access”).
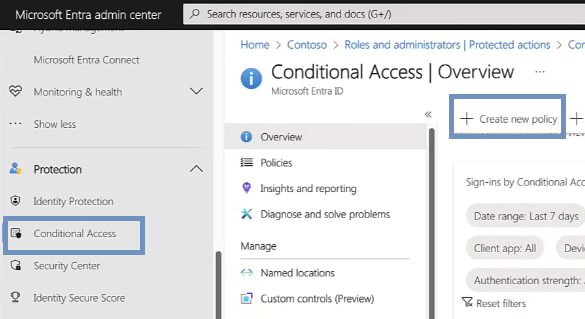
- Assign Users or Groups
3 - Under Users, select Global Administrators.
- Configure Cloud Apps or Actions
4 - Under Target resources, select Microsoft Entra ID.
- Set Conditions for Untrusted Locations
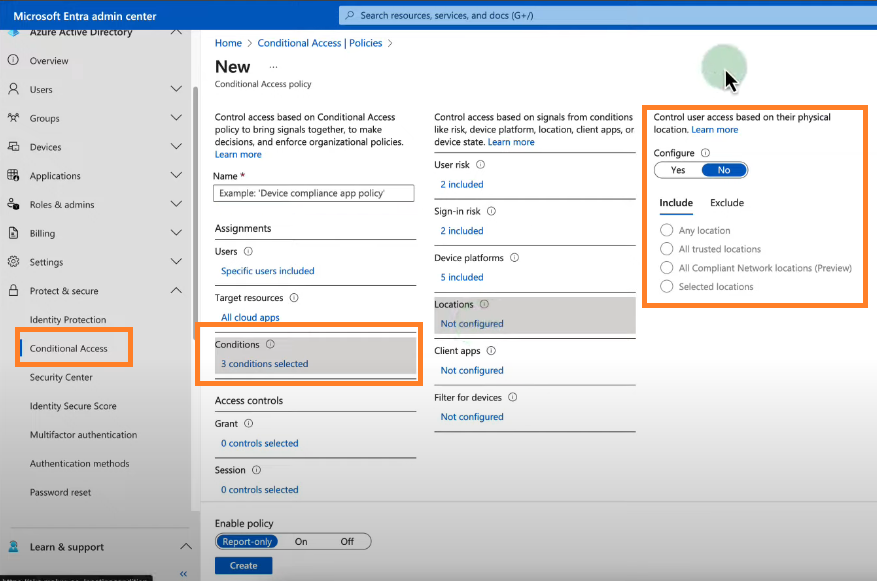
5 - Under Conditions → Locations, select Exclude trusted locations (e.g., corporate offices, hospitals).
- Select Include Any location (so the policy applies everywhere except trusted locations).
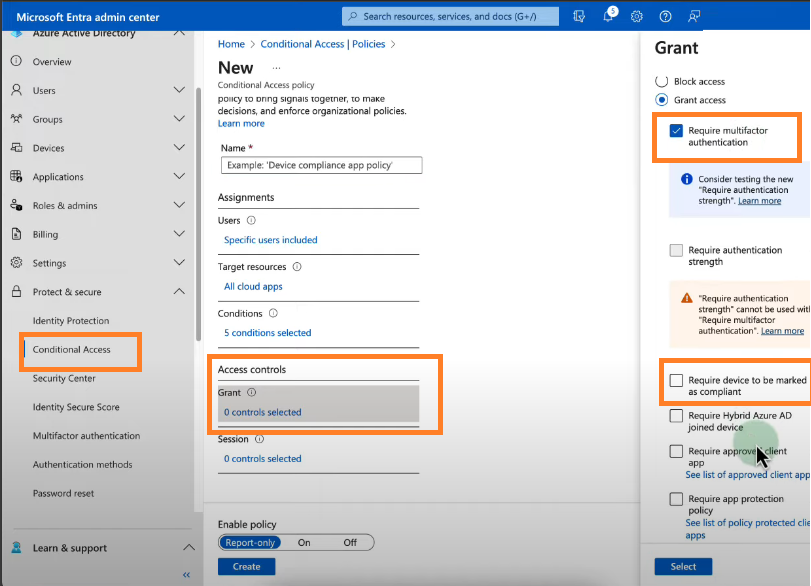
- Require MFA and Entra ID-Joined Device
6 - Under Access Controls → Grant, select:
- Require Multi-Factor Authentication
- Require device to be marked as compliant (for Entra ID-joined devices)
7 - Enable Policy
- Set Enable policy to On.
- Click Create to activate the policy.
Exam Tip: Why This Matters for AZ-104?
- Conditional Access is a key topic in AZ-104, and understanding real-world applications will help you in scenario-based questions.
- Remember: Editing MFA settings alone does not create a Conditional Access policy.
- Conditional Access requires policies that define conditions (e.g., location, device compliance) and controls (e.g., MFA, block access).